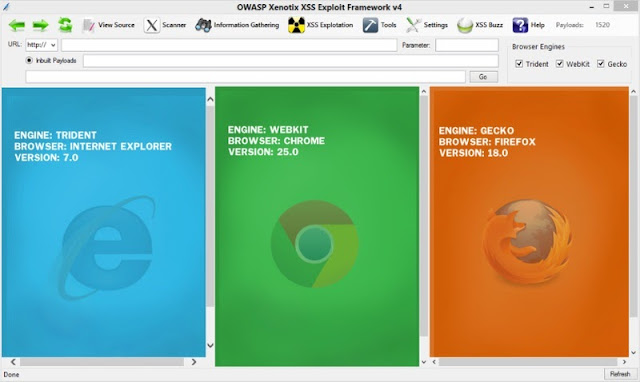
OWASP Xenotix XSS Exploit Framework is an advanced Cross Site Scripting (XSS) vulnerability detection and exploitation framework. It provides Zero False Positive scan results with its unique Triple Browser Engine (Trident, WebKit, and Gecko) embedded scanner. It is claimed to have the world’s 2nd largest XSS Payloads of about 1600+ distinctive XSS Payloads for effective XSS vulnerability detection and WAF Bypass. Xenotix Scripting Engine allows you to create custom test cases and addons over the Xenotix API. It is incorporated with a feature rich Information Gathering module for target Reconnaissance. The Exploit Framework includes offensive XSS exploitation modules for Penetration Testing and Proof of Concept creation.
Following are the V5 Additions
- Xenotix Scripting Engine
- Xenotix API
- V4.5 Bug Fixes
- GET Network IP (Information Gathering)
- QR Code Generator for Xenotix xook
- HTML5 WebCam Screenshot(Exploitation Module)
- HTML5 Get Page Screenshot (Exploitation Module)
- Find Feature in View Source.
- Improved Payload Count to 1630
- Name Changes
Xenotix Scripting Engine and API
This release features the Xenotix Scripting Engine that works on the top of Xenotix API. The Scripting Engine helps you to create tools and test cases on the go based on your requirements. There are situations when you have to go the manual way and since the ruleset set of an automated tool is not applicable in certain situations. Xenotix Scripting Engine powered by Xenotix API come into your rescue. Now you can make sure your tool works based on your requirements. Apply your Python scripting skills on the latest Scripting Engine.Xenotix API features
- 1630 XSS Detection Payloads.
- An inbuilt GET Request XSS Fuzzer for Intelligent and Fast XSS Vulnerability Detection.
- Analyze Response in Trident and Gecko Web Engines to make sure that there are no false positives.
- Interact with Web Engines from the scope of a Python Script.
- Make GET and POST Requests with one liner codes.
Reguirements
- Microsoft .NET Framework 4.0 http://www.microsoft.com/en-in/download/details.aspx?id=17718
- IronPython 2.7.3 http://ironpython.codeplex.com/downloads/get/423690